In September 1960, two U.S. National Security Agency (NSA) cryptologists, William Hamilton Martin and Bernon F. Mitchell, defected to the Soviet Union. A secret 1963 NSA study said that: "Beyond any doubt, no other event has had, or is likely to have in the future, a greater impact on the Agency's security program."Martin and Mitchell met while serving in the U.S. Navy in Japan in the early 1950s and both joined the NSA on the same day in 1957. They defected together to the Soviet Union in 1960 and, at a Moscow press conference, revealed and denounced various U.S. policies, especially provocative incursions into the air space of other nations and spying on America's own allies. Underscoring their apprehension of nuclear war, they said: "we would attempt to crawl to the moon if we thought it would lessen the threat of an atomic war."Within days of the press conference, citing a trusted source, Congressman Francis E. Walter, chairman of the House Un-American Activities Committee (HUAC), said Martin and Mitchell were "sex deviates", prompting sensational press coverage. U.S. officials at the National Security Council privately shared their assumption that the two were part of a traitorous homosexual network. Classified NSA investigations, on the other hand, determined the pair had "greatly inflated opinions concerning their intellectual attainments and talents" and had defected to satisfy social aspirations. The House Un-American Activities Committee publicly intimated its interpretation of the relationship between Martin and Mitchell as homosexual and that reading guided the Pentagon's discussion of the defection for decades.
Cryptography, or cryptology (from Ancient Greek: κρυπτός, romanized: kryptós "hidden, secret"; and γράφειν graphein, "to write", or -λογία -logia, "study", respectively), is the practice and study of techniques for secure communication in the presence of adversarial behavior. More generally, cryptography is about constructing and analyzing protocols that prevent third parties or the public from reading private messages; various aspects in information security such as data confidentiality, data integrity, authentication, and non-repudiation are central to modern cryptography. Modern cryptography exists at the intersection of the disciplines of mathematics, computer science, electrical engineering, communication science, and physics. Applications of cryptography include electronic commerce, chip-based payment cards, digital currencies, computer passwords, and military communications.
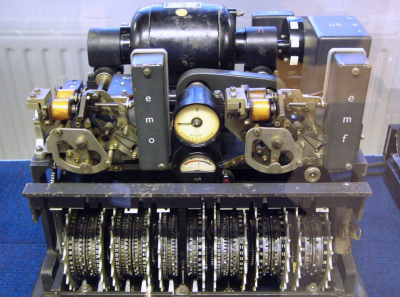
Cryptography prior to the modern age was effectively synonymous with encryption, converting information from a readable state to unintelligible nonsense. The sender of an encrypted message shares the decoding technique only with intended recipients to preclude access from adversaries. The cryptography literature often uses the names Alice ("A") for the sender, Bob ("B") for the intended recipient, and Eve ("eavesdropper") for the adversary. Since the development of rotor cipher machines in World War I and the advent of computers in World War II, cryptography methods have become increasingly complex and their applications more varied.
Modern cryptography is heavily based on mathematical theory and computer science practice; cryptographic algorithms are designed around computational hardness assumptions, making such algorithms hard to break in actual practice by any adversary. While it is theoretically possible to break into a well-designed system, it is infeasible in actual practice to do so. Such schemes, if well designed, are therefore termed "computationally secure"; theoretical advances (e.g., improvements in integer factorization algorithms) and faster computing technology require these designs to be continually reevaluated, and if necessary, adapted. Information-theoretically secure schemes that provably cannot be broken even with unlimited computing power, such as the one-time pad, are much more difficult to use in practice than the best theoretically breakable, but computationally secure, schemes.
The growth of cryptographic technology has raised a number of legal issues in the Information Age. Cryptography's potential for use as a tool for espionage and sedition has led many governments to classify it as a weapon and to limit or even prohibit its use and export. In some jurisdictions where the use of cryptography is legal, laws permit investigators to compel the disclosure of encryption keys for documents relevant to an investigation. Cryptography also plays a major role in digital rights management and copyright infringement disputes in regard to digital media.

1960Jun, 25
Two cryptographers working for the United States National Security Agency left for vacation to Mexico, and from there defected to the Soviet Union.
Choose Another Date
Events on 1960
- 17Mar
Bay of Pigs Invasion
U.S. President Dwight D. Eisenhower signs the National Security Council directive on the anti-Cuban covert action program that will ultimately lead to the Bay of Pigs Invasion. - 21Apr
Rio de Janeiro
Brasília, Brazil's capital, is officially inaugurated. At 09:30, the Three Powers of the Republic are simultaneously transferred from the old capital, Rio de Janeiro. - 9May
Combined oral contraceptive pill
The Food and Drug Administration announces it will approve birth control as an additional indication for Searle's Enovid, making Enovid the world's first approved oral contraceptive pill. - 4Jul
Flag of the United States
Due to the post-Independence Day admission of Hawaii as the 50th U.S. state on August 21, 1959, the 50-star flag of the United States debuts in Philadelphia, almost ten and a half months later (see Flag Act). - 29Oct
Muhammad Ali
In Louisville, Kentucky, Cassius Clay (who later takes the name Muhammad Ali) wins his first professional fight.

 English
English  español
español  français
français  português
português  русский
русский  العربية
العربية  简体中文
简体中文